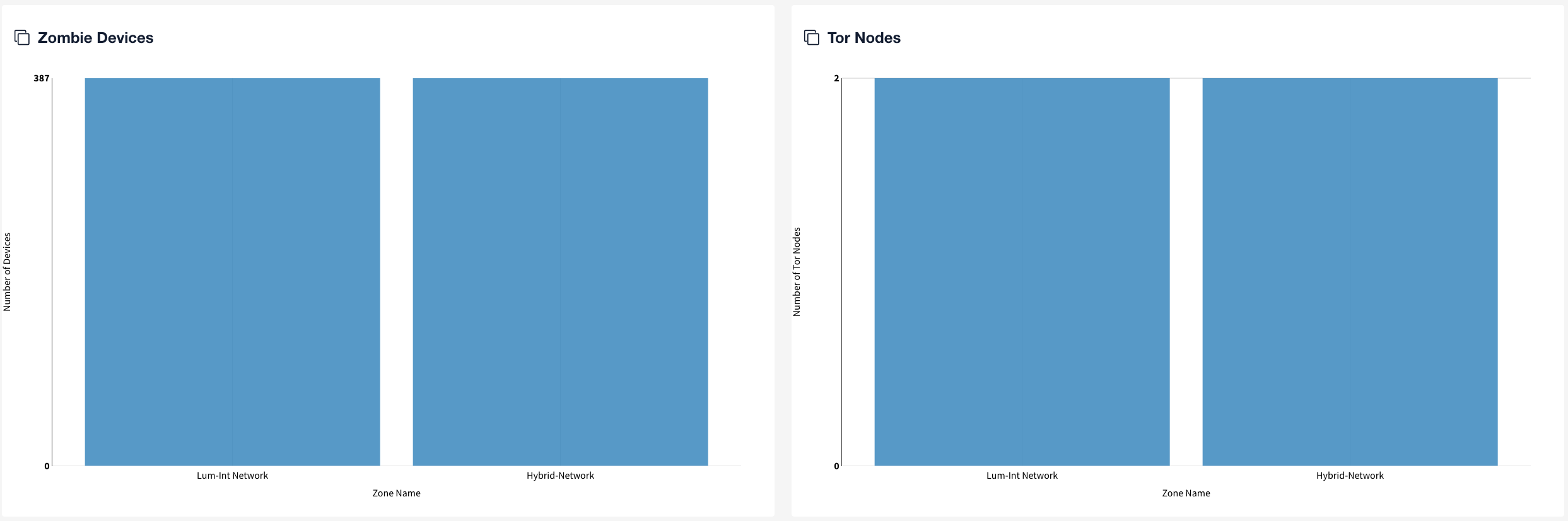
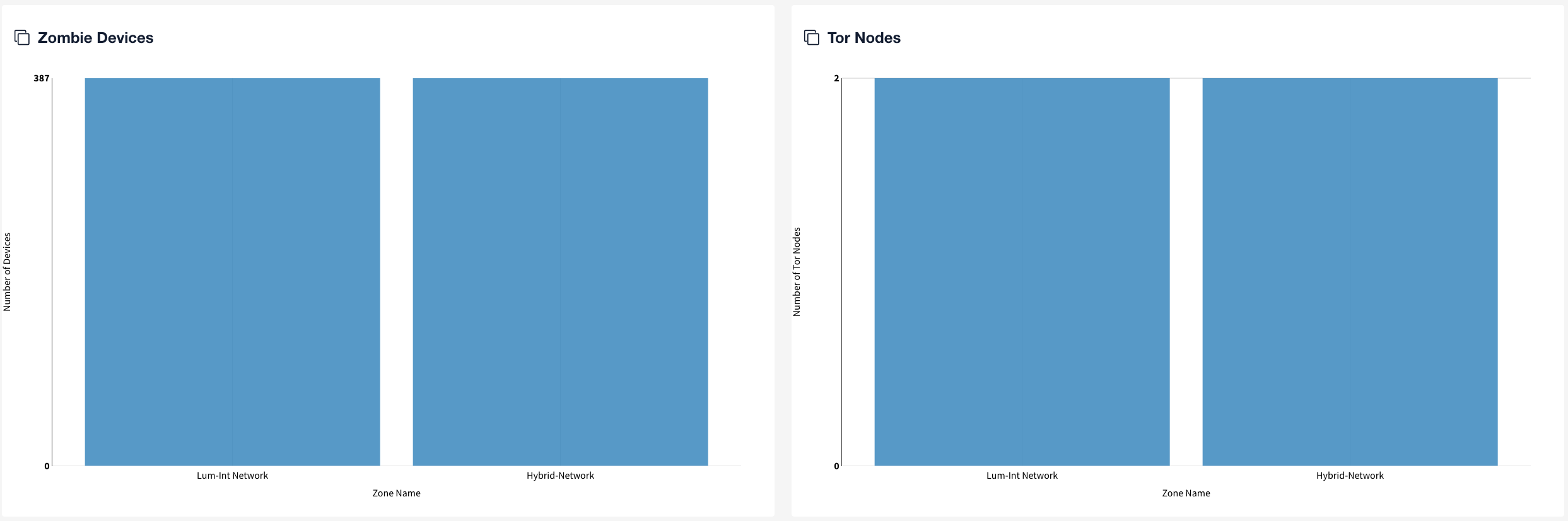
- Zombie Devices
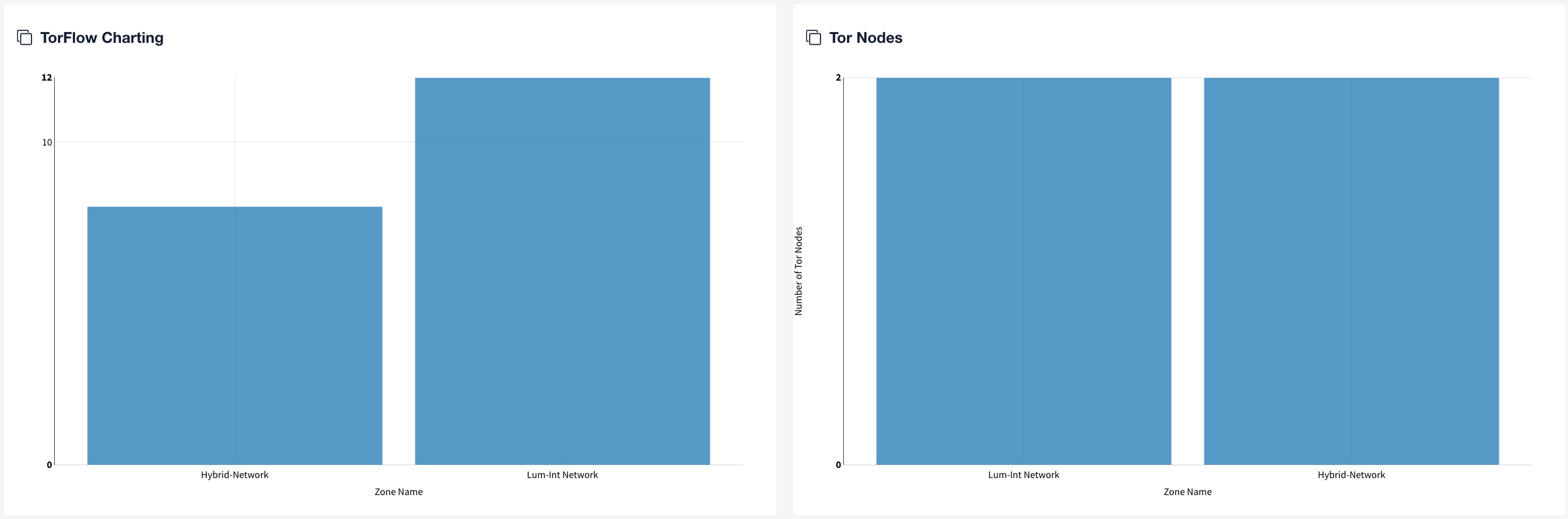
- Tor Nodes
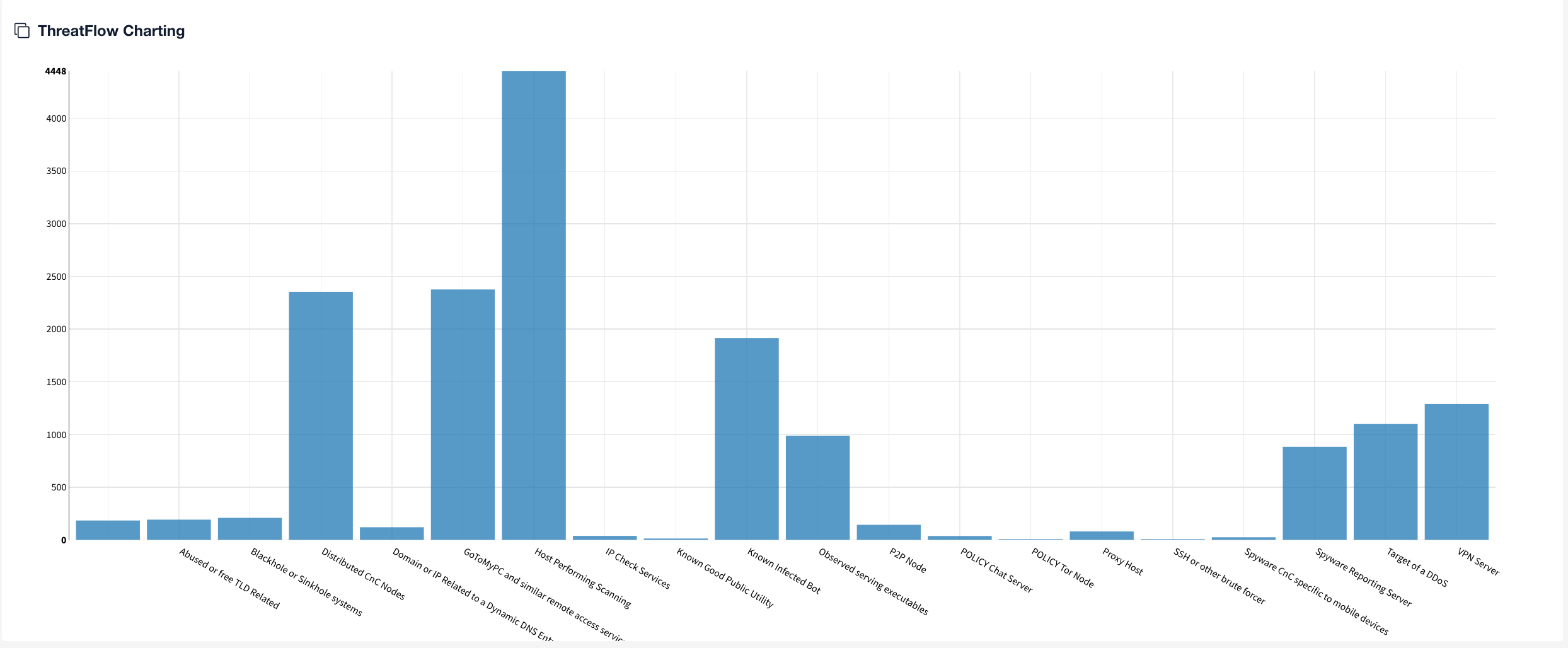
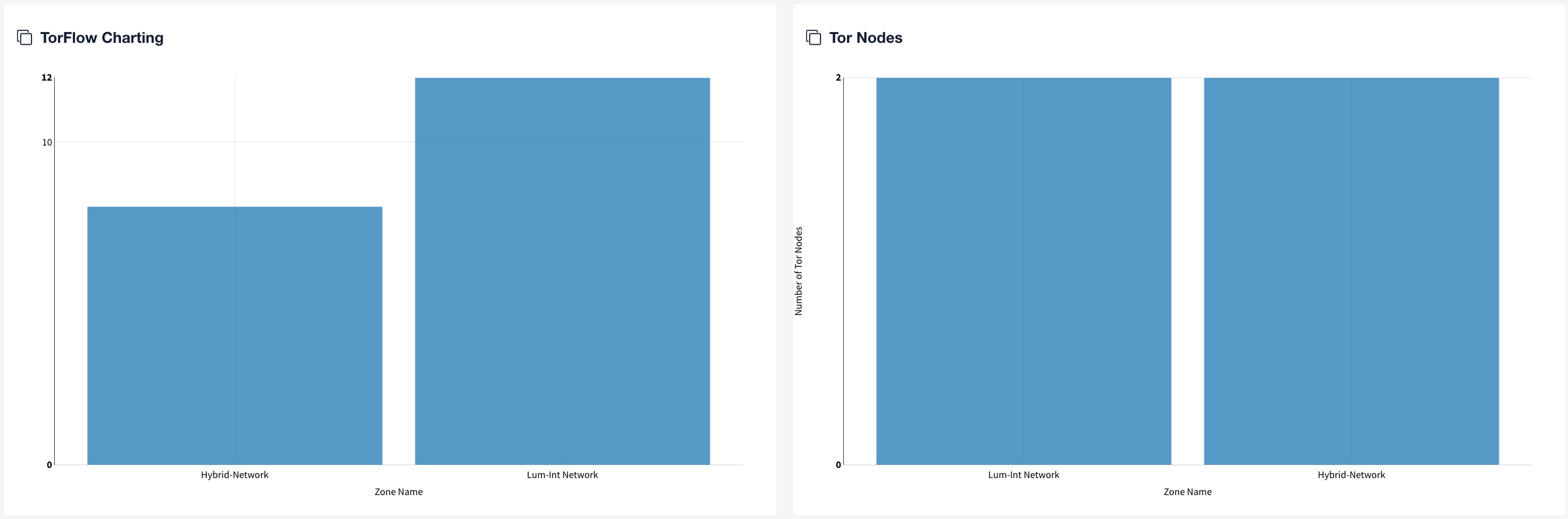
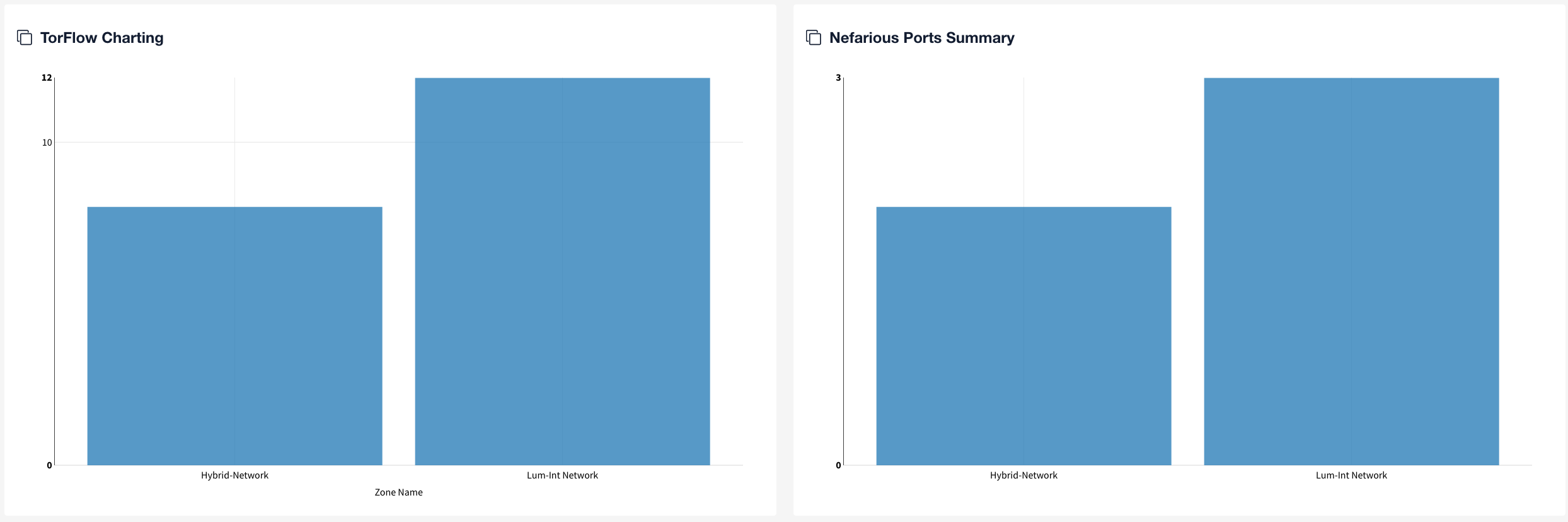
- TorFlow Charting
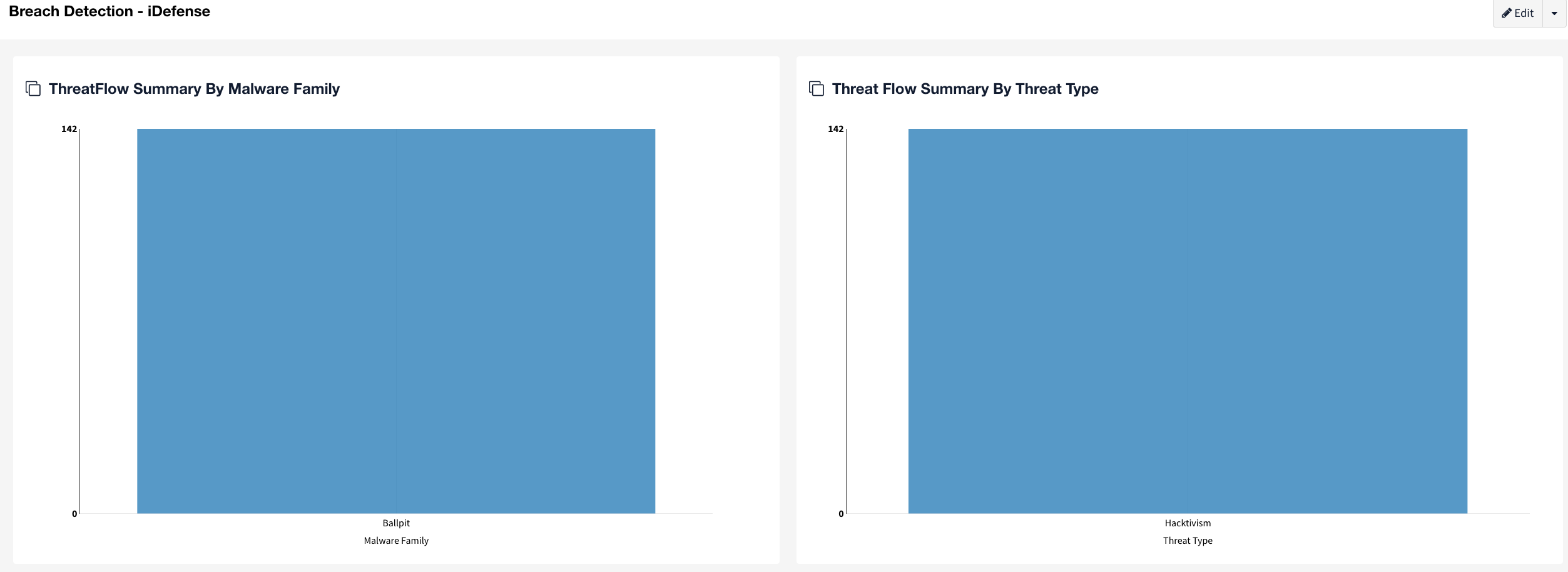
- Nefarious Ports
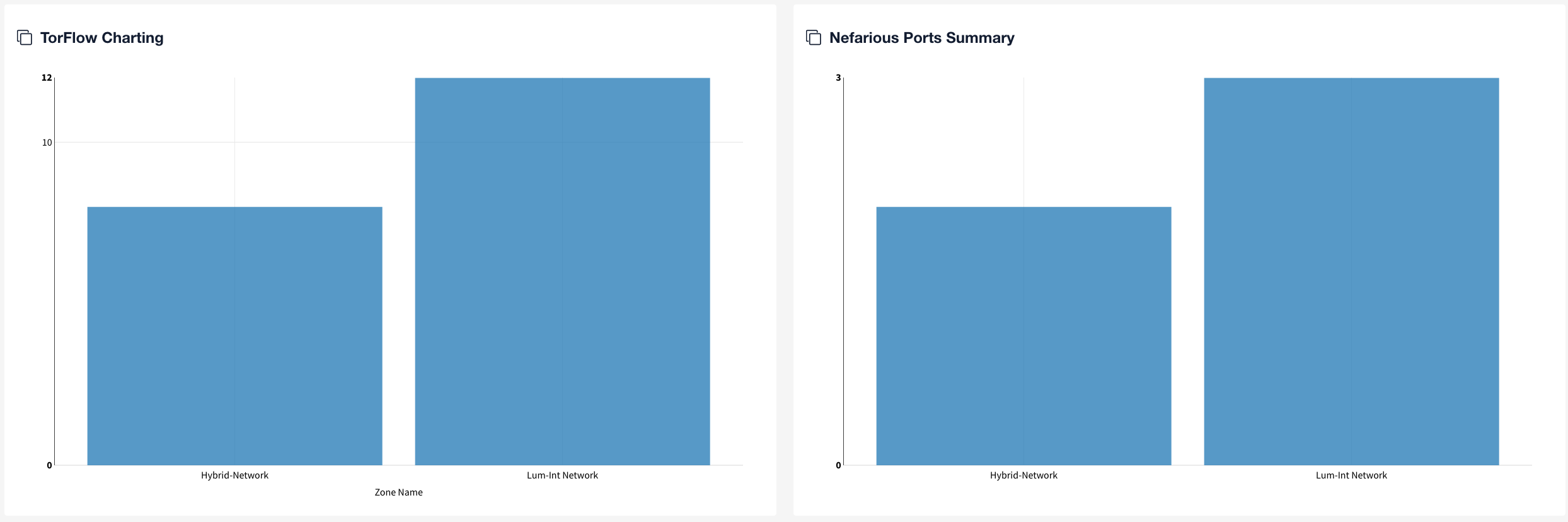

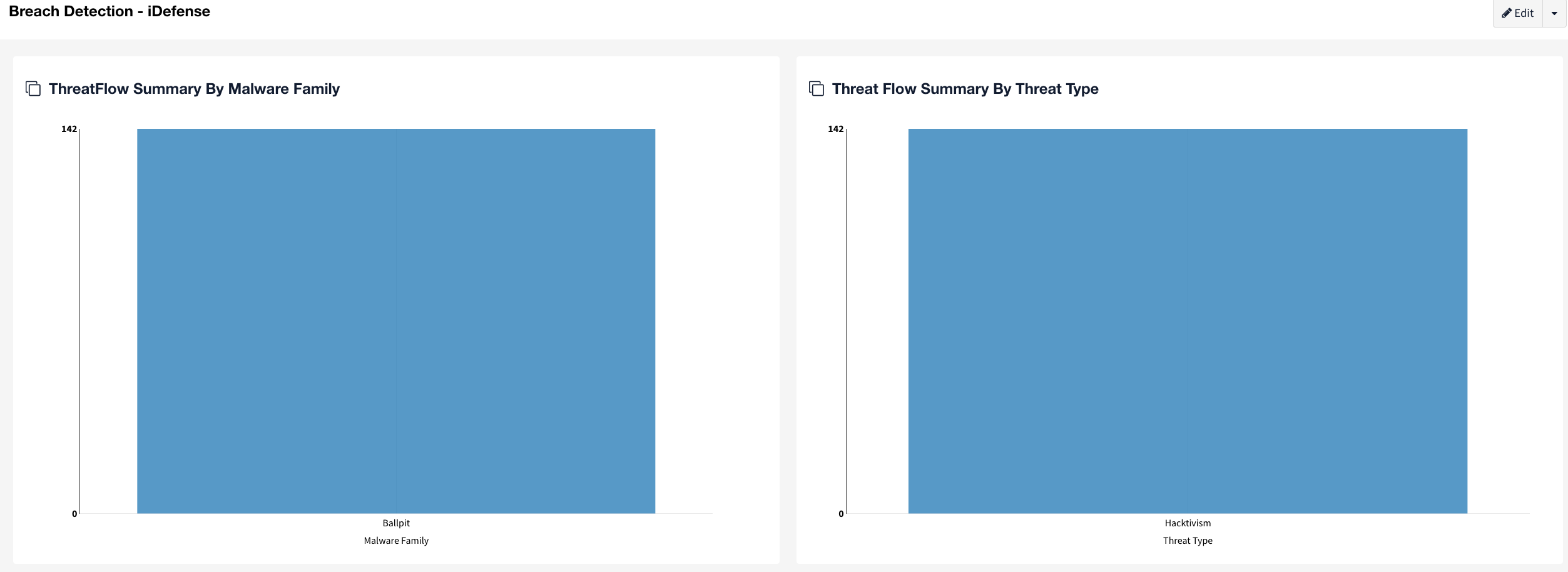
The Breach Detection dashboards, Breach Detection and Breach Detection - iDefense, are powered primarily by the iDefense, and Emerging Threats integrations (which is open source), but are also affected by the Tor, ISC Port and Gigamon NetFlow feeds, enable you to monitor all Spectre zones relative to security threats.

Refresh your browser to update all widgets on the Breach Detection dashboard. Or, set an interval at which to automatically refresh a selected widget on the dashboard (Edit > Gear icon > Edit Widget Settings). |
Are your network's active security controls preventing communications to known zombie and command-and-control (C2) networks and servers? This widget helps you watch in real time for exfiltration to known bad servers and networks that were identified via open-source and closed-source intelligence feeds and repositories.
If CTP finds access to C2/Zombie machines, the following may be occurring:
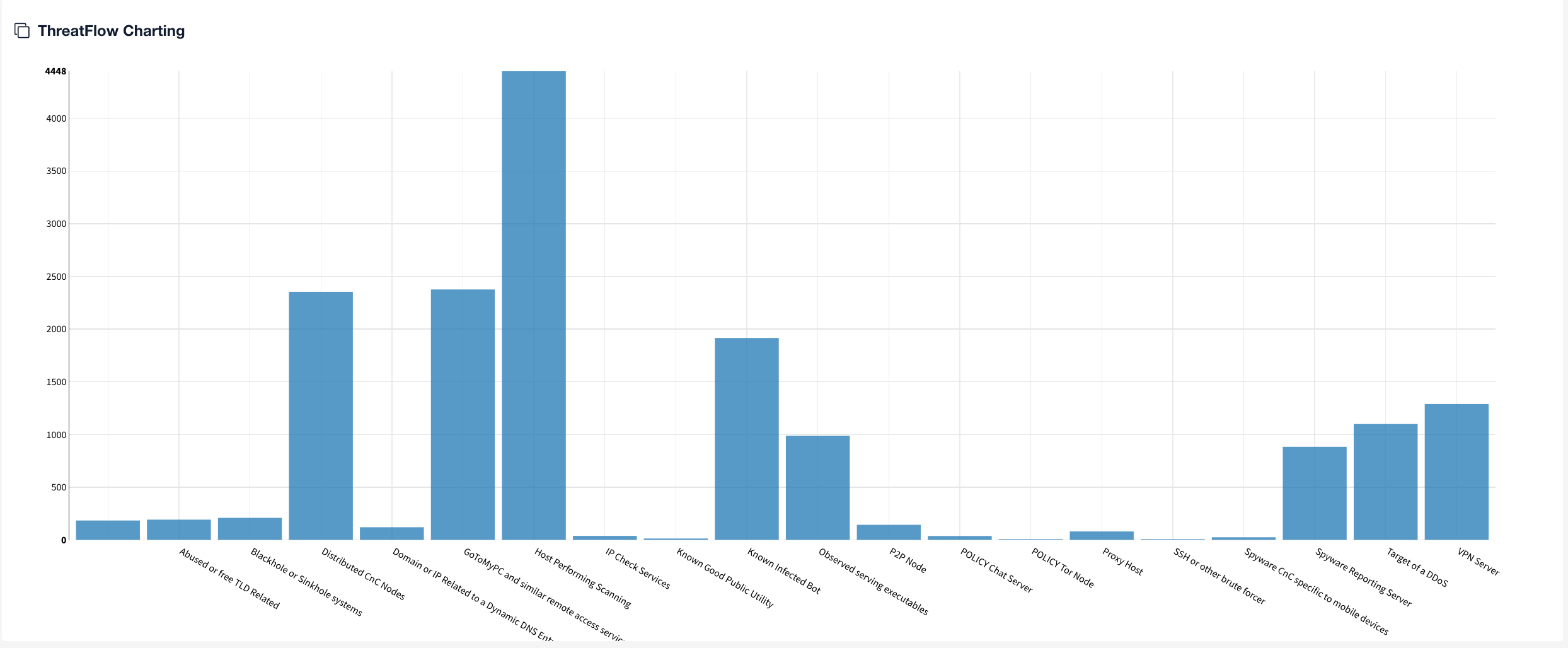
ThreatFlow has the following dependencies and requirements:
Contact your Solutions Architect and Support if you need assistance with any of these items. |
The ThreatFlow view shows the intersection of threat intelligence feeds and NetFlow data.
This dashboard view is designed to highlight any devices found with open known-vulnerable ports. After nefarious ports candidate devices have been identified, your organization is advised to manually validate any exploit activity and take action to remediate compromised assets.