The Breach Detection dashboards, Breach Detection and Breach Detection - iDefense, are powered primarily by the iDefense, and Emerging Threats integrations (which is open source), but are also affected by the Tor, ISC Port and NetFlow feeds, enable enabling you to monitor all Lumeta Asset Manager zones relative to security threats.
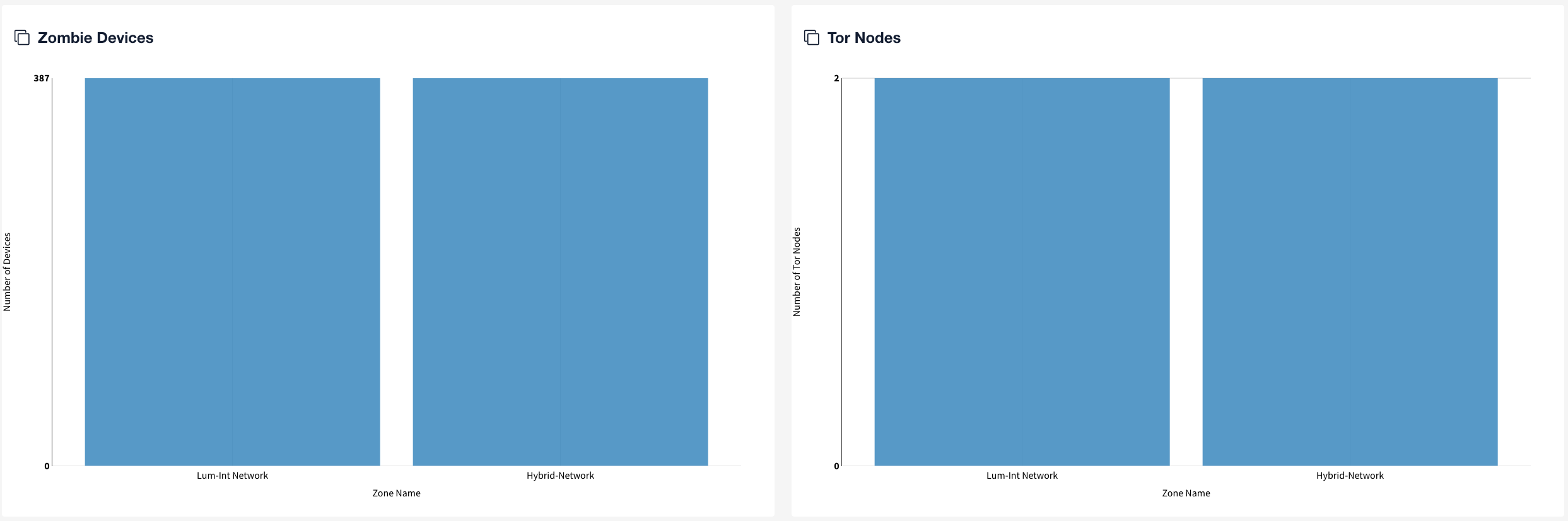
- Both Dashboards - In LumetaAsset Manager, both dashboards present data in these categories:
- Zombie Devices
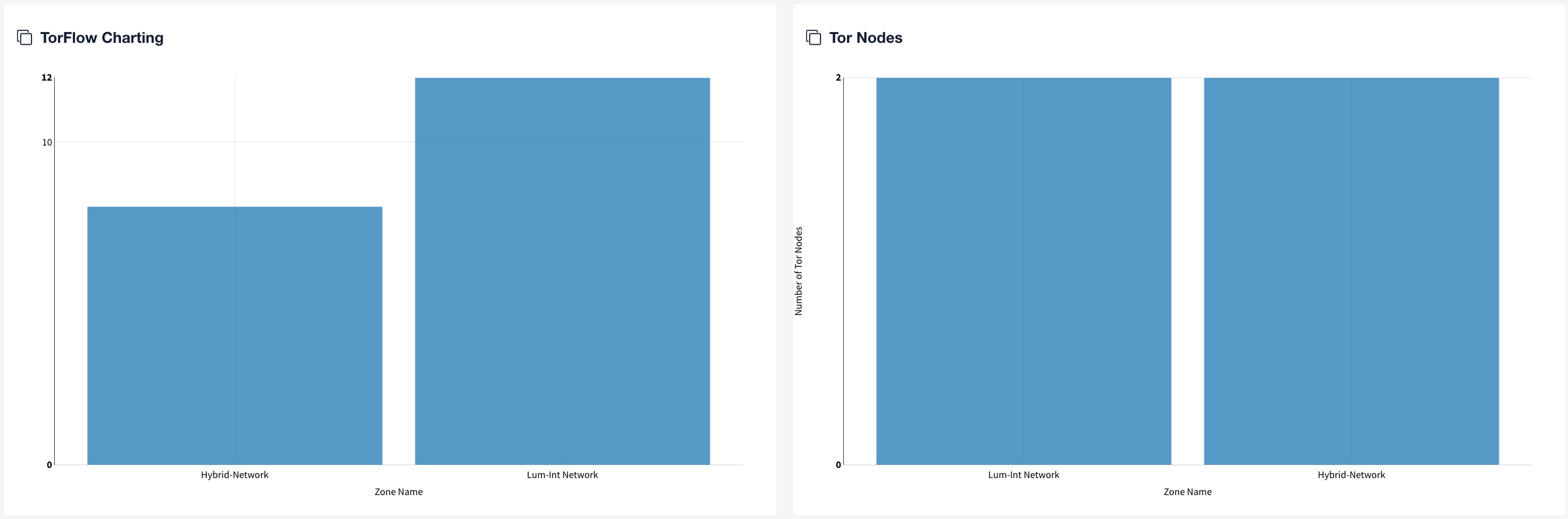
- Tor Nodes
- TorFlow Charting
- Nefarious Ports
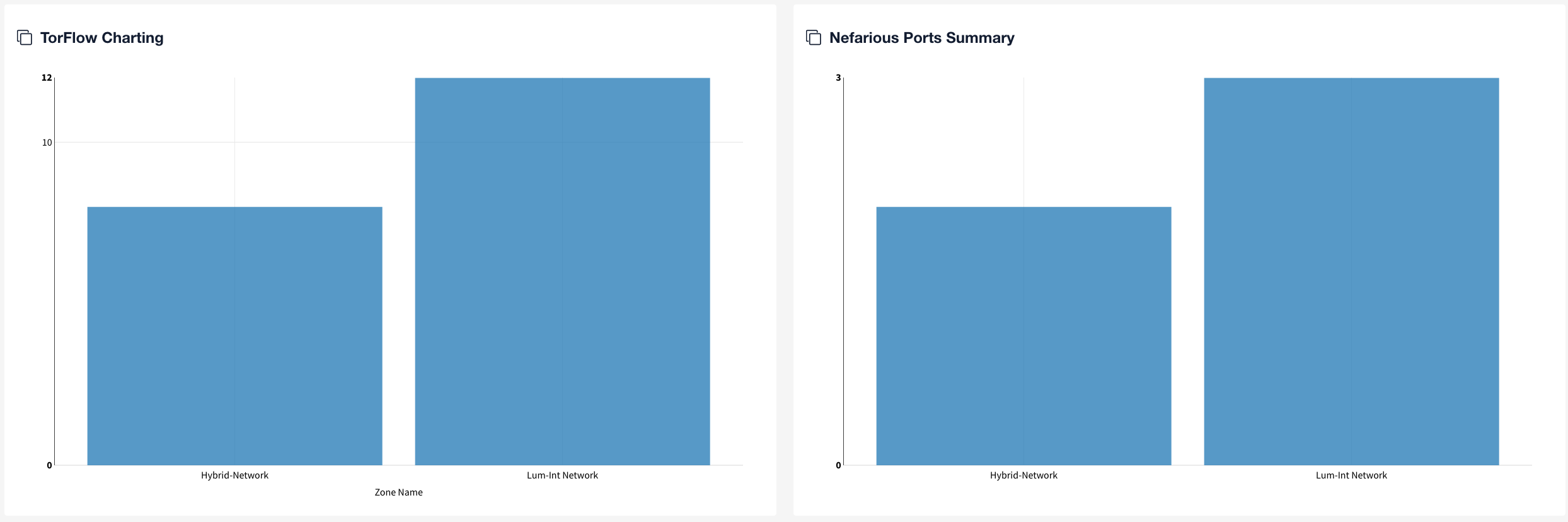
- Breach Detection Dashboard: The Breach Detection dashboard also uniquely presents data fed by the Emerging Threats integration in the ThreatFlow Charting widget.
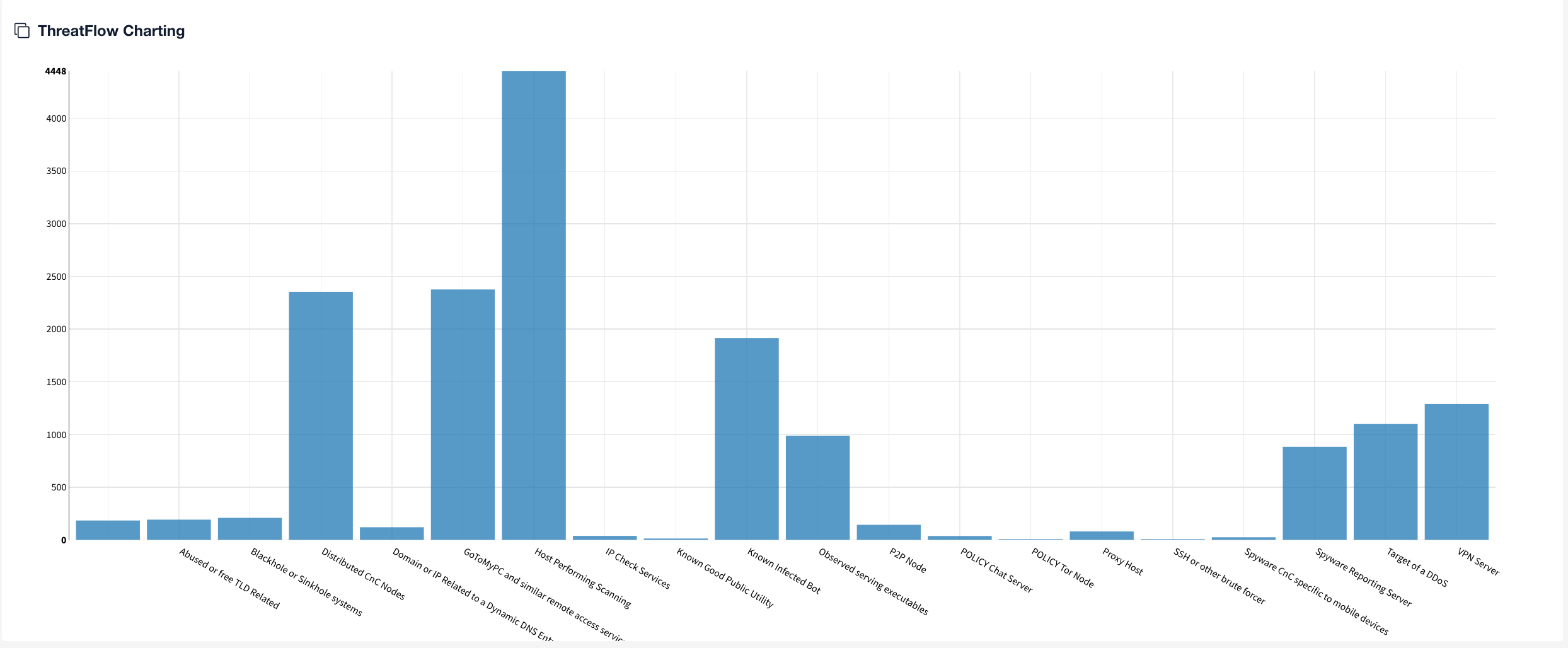
- Breach Detection Dashboard - iDefense: Presents unique data from iDefense such as Threatflow by Malware Family and Threatflow by Threat Type.
| Tip | ||
|---|---|---|
| ||
Refresh your browser to update all widgets on the Breach Detection dashboard. Or, set an interval at which to automatically refresh a selected widget on the dashboard (Edit > Gear Settings icon > Edit Widget Settings). |
...
- Firewall rules are not effective at limiting outbound sessions over protocols known to be at-risk.
- Firewalls/NGFW/IPS/DLP solutions are not effective at limiting or blocking access to known bad networks or servers.
- Given that one or more egress points let traffic out, security architecture is not uniform across the enterprienterprise.
ThreatFlow Charting
| Warning | ||
|---|---|---|
| ||
ThreatFlow has the following dependencies and requirements:
Contact your Solutions Architect and Support if you need assistance with any of these items. |
...